AIS Password: What is the password to open Annual Information Statement (AIS) after downloading - The Economic Times
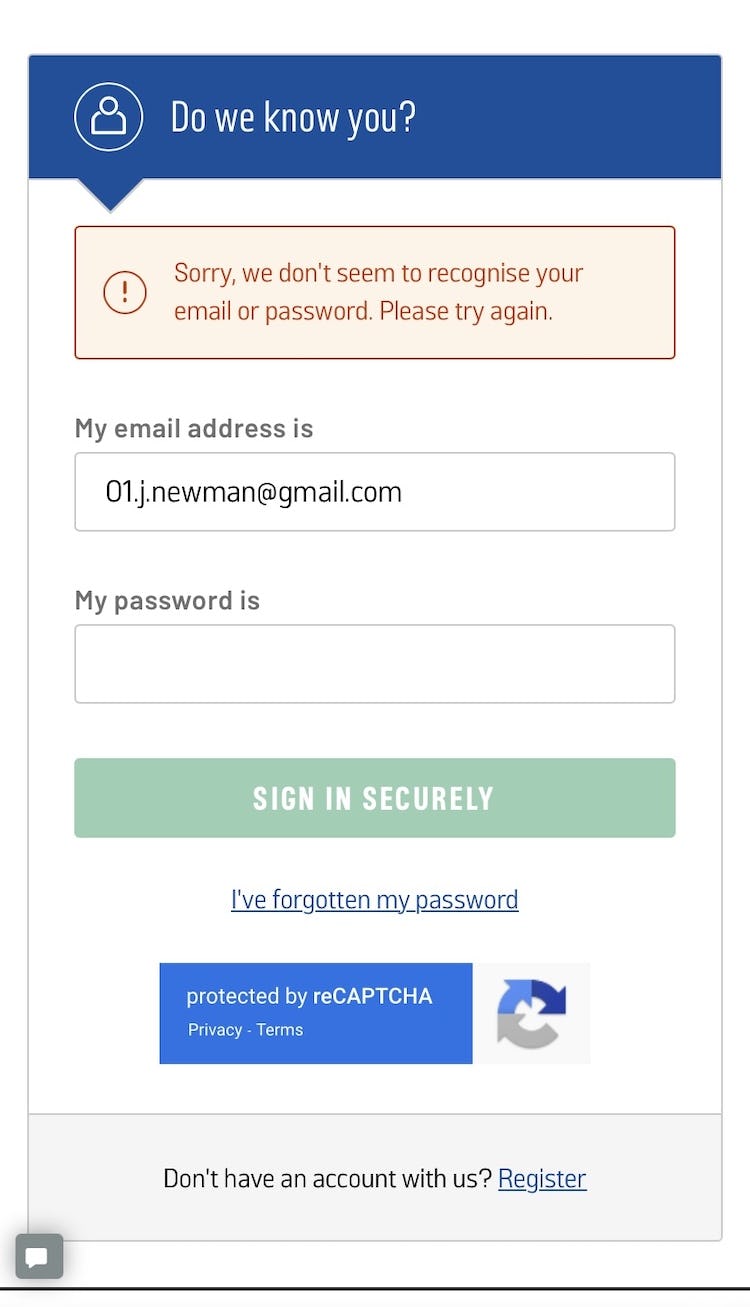
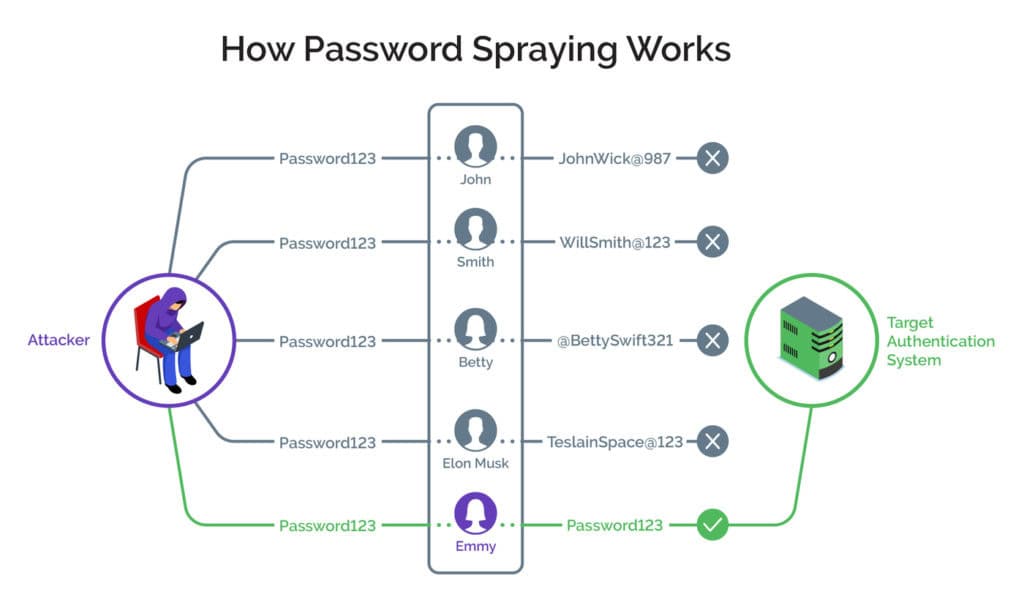
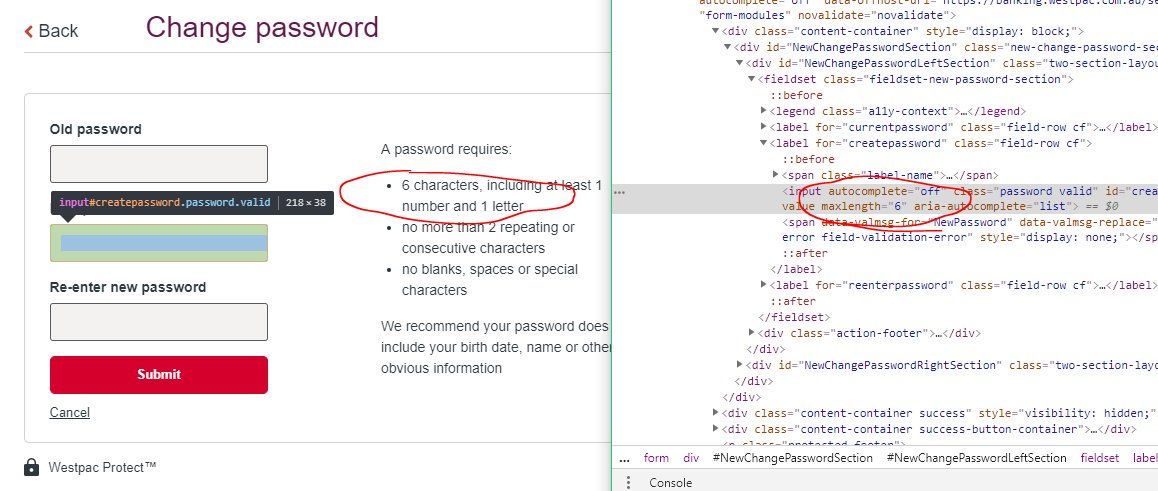
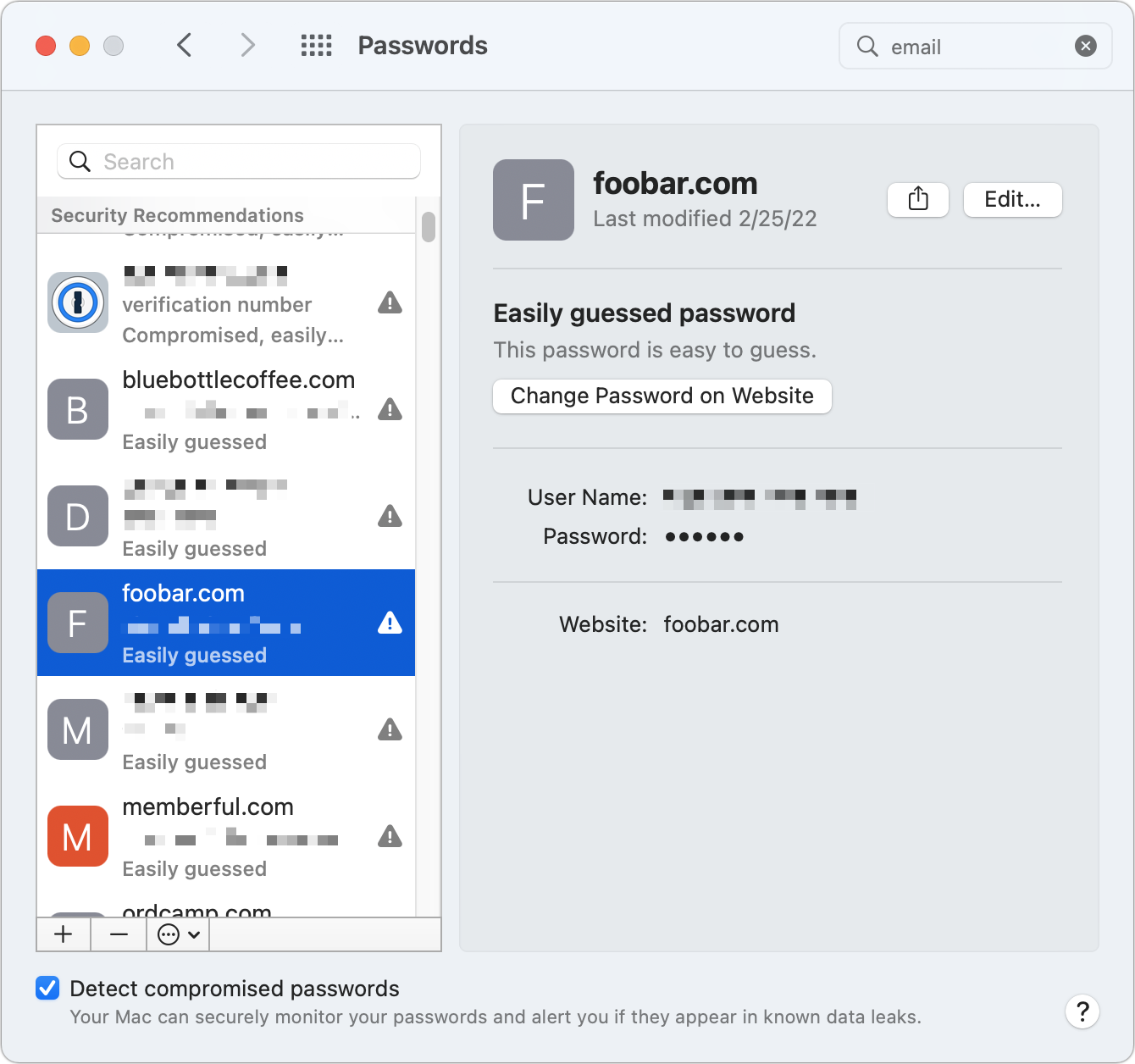
Avoid Unnecessarily Complex Password-Creation Requirements (82% Don't) – Articles – Baymard Institute
![PDF] DATA HIDING IN IMAGE BASED AUTHENTICATION USING COMBINATION OF ZERO-KNOWLEDGE PROTOCOL AND STEGANOGRAPHY NURUL NADZIRAH BT ADNAN | Semantic Scholar PDF] DATA HIDING IN IMAGE BASED AUTHENTICATION USING COMBINATION OF ZERO-KNOWLEDGE PROTOCOL AND STEGANOGRAPHY NURUL NADZIRAH BT ADNAN | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/208e0b8c6778e7f2d418dcca74fd29c1705bb6a1/40-Figure1-1.png)
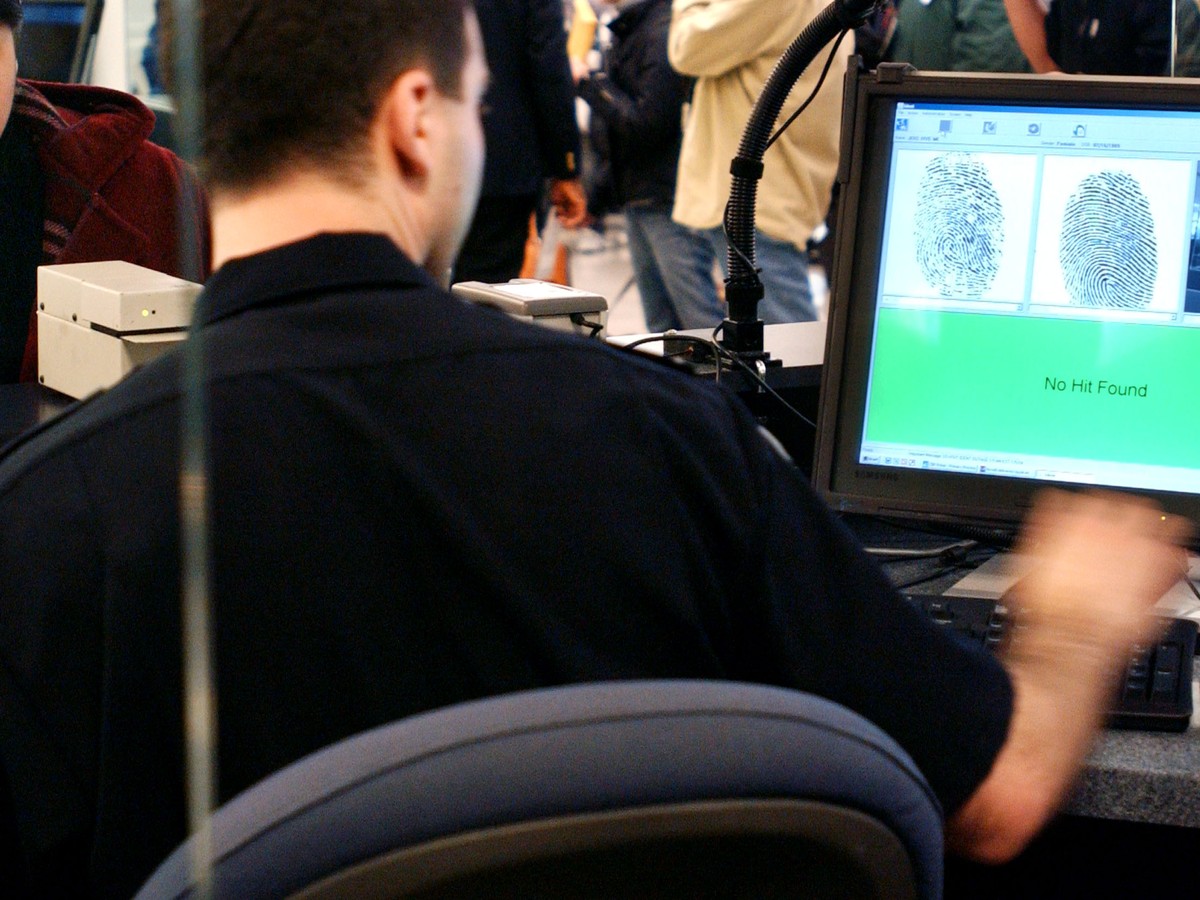
PDF] DATA HIDING IN IMAGE BASED AUTHENTICATION USING COMBINATION OF ZERO-KNOWLEDGE PROTOCOL AND STEGANOGRAPHY NURUL NADZIRAH BT ADNAN | Semantic Scholar

The Man Tries To Pick Up Blocks with the Word Data. Digital Data Integrity and Security Vulnerability Concept Stock Photo - Image of data, internet: 211493740

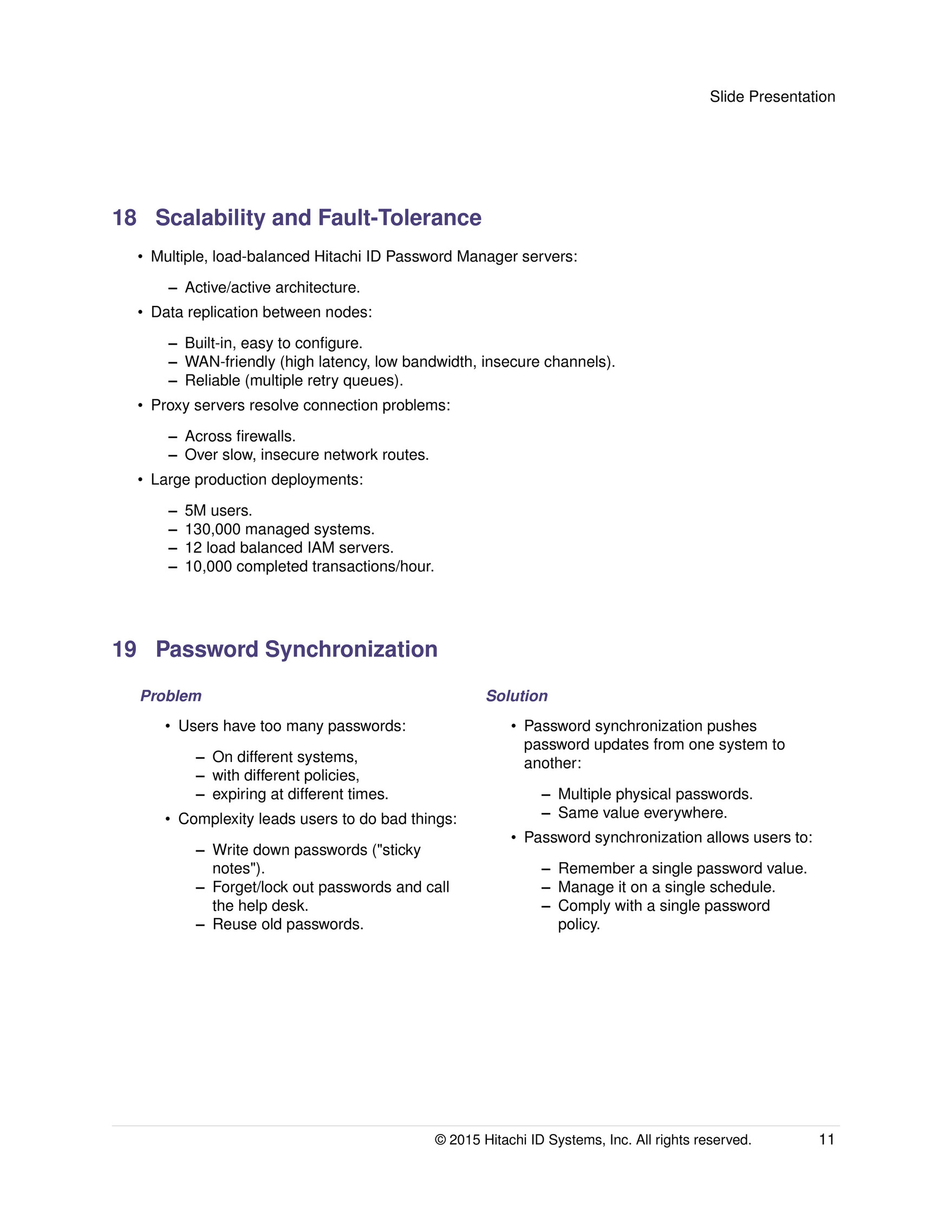
Lightweight and Secure Password Based Smart Home Authentication Protocol: LSP-SHAP | springerprofessional.de

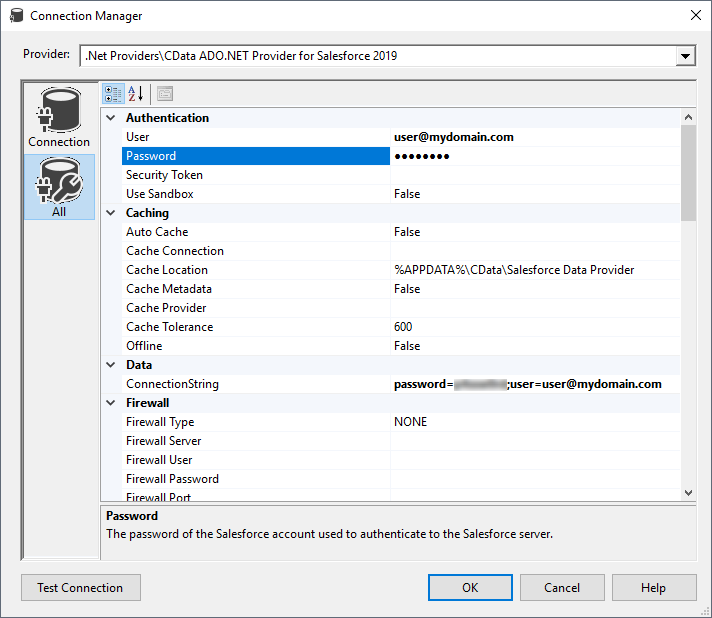
Avoid Unnecessarily Complex Password-Creation Requirements (82% Don't) – Articles – Baymard Institute